Rhino security labs is a top penetration testing and security assessment firm with a focus on cloud pentesting aws gcp azure network pentesting web application pentesting and phishing.
Aws s3 security vulnerabilities.
With manual deep dive engagements we identify security vulnerabilities which put clients at risk.
Aws s3 buckets are exposing vast quantities of sensitive business data according to a new report from truffle security.
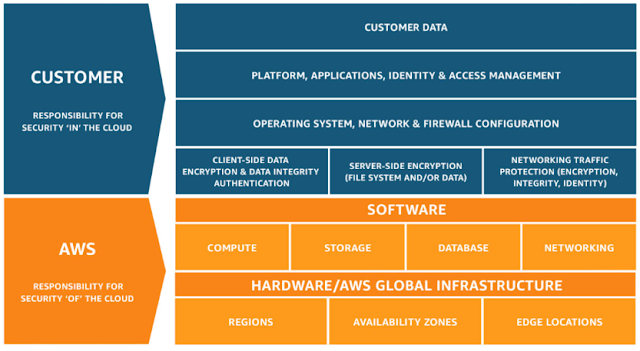
To learn about the compliance programs that apply to amazon s3 see aws services in scope by compliance program.
The effectiveness of our security is regularly tested and verified by third party auditors as part of the aws compliance programs.
Detectify scans for s3 misconfigurations with a severity range between 4 4 9 on the cvss scale.
The 6 vulnerability types are.
This is the most common type of cloud security vulnerability.
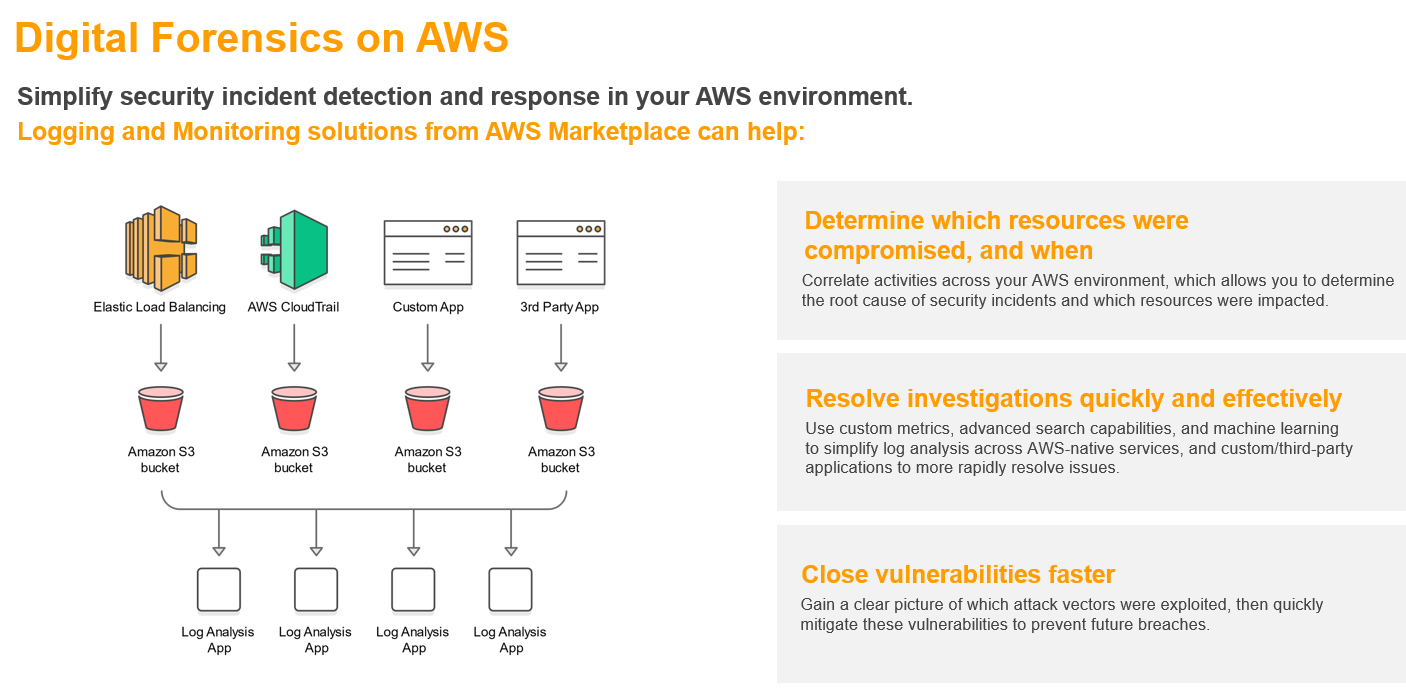
The following security best practices also address configuration and vulnerability analysis in amazon s3.
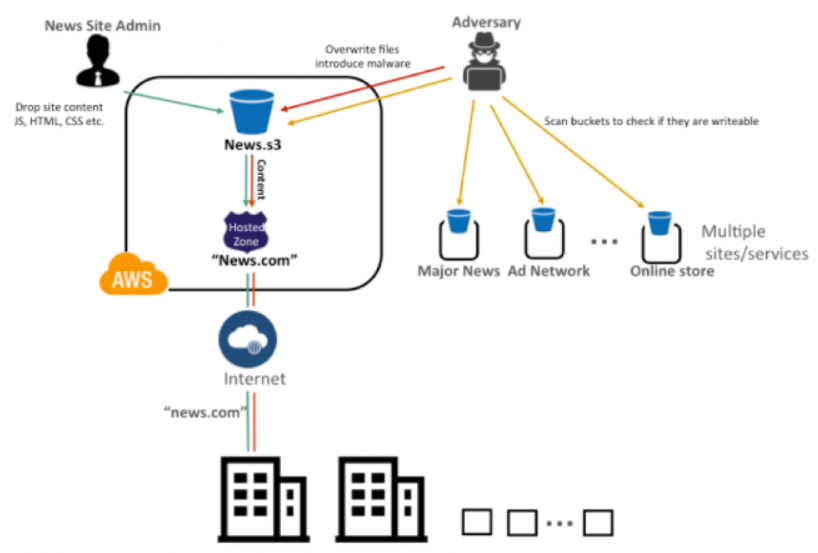
List permissions on compute resources.
In our last aws penetration testing post we explored what a pentester could do after compromising credentials of a cloud server in this installment we ll look at an amazon web service aws instance from a no credential situation and specifically potential security vulnerabilities in aws s3 simple storage buckets.
Identify and audit all your amazon s3 buckets enable aws config.
It hurts because it is self inflicted.
Aws s3 bucket vulnerabilities could be wormable.
If you would like to report a vulnerability or have a security concern regarding aws.
Aws s3 common vulnerabilities.
Another reason is the lack of training.
Amazon s3 bucket allows for full anonymous access amazon s3 bucket allows for arbitrary file listing.
Amazon web services aws.
S3 bucket configured to allow anonymous users to list read or write data to the bucket.
They are all placed in the security misconfiguration category in the detectify tool.
Continuing from our previous blog basics of aws s3 bucket penetration testing and once you have configured the aws cli setup we will move to exploit the aws s3 bucket vulnerabilities.